AWS CDK Security Best Practices
.MP4, AVC, 1280x720, 30 fps | English, AAC, 2 Ch | 25m | 69.2 MB
Instructor: Elle Krout
.MP4, AVC, 1280x720, 30 fps | English, AAC, 2 Ch | 25m | 69.2 MB
Instructor: Elle Krout
Knowing how to secure your AWS CDK-backed applications can save you a lot of woe in the future. This course will teach you how to leverage best practices, smart aspect use, and AWS Config to ensure you’re on top of keeping your apps secure.
What you'll learn
Protect your AWS Cloud-Development Kit-backed applications from threats, accidents, and other security woes by leveraging intelligent security principles. In this course, AWS CDK Security Best Practices, you’ll learn to secure your CDK applications.
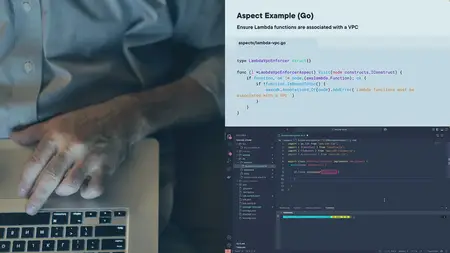
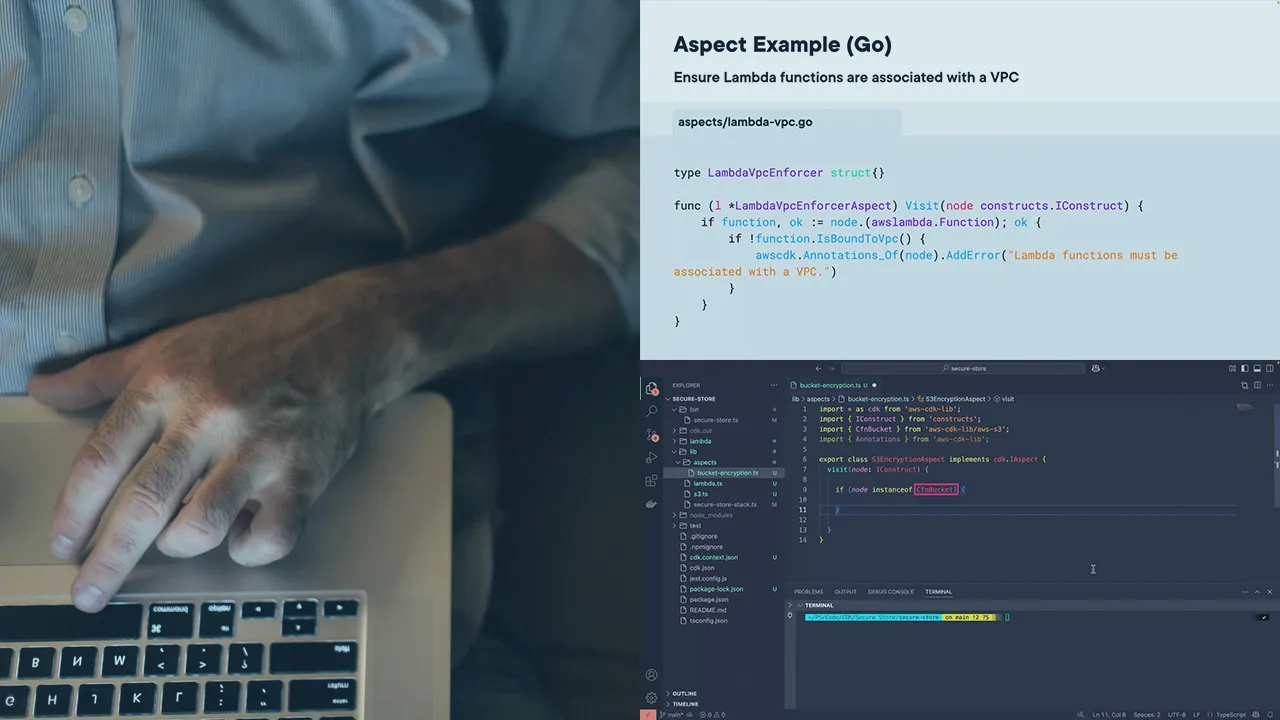
First, you’ll explore how to use CDK aspects to prevent potential problems. Next, you’ll discover how to use AWS Config to enforce compliance and detect issues. Finally, you’ll learn some general best practices for security CDK applications.
When you’re finished with this course, you’ll have the skills and knowledge of securing your CDK apps needed to rest easy knowing they’re protected once deployed.